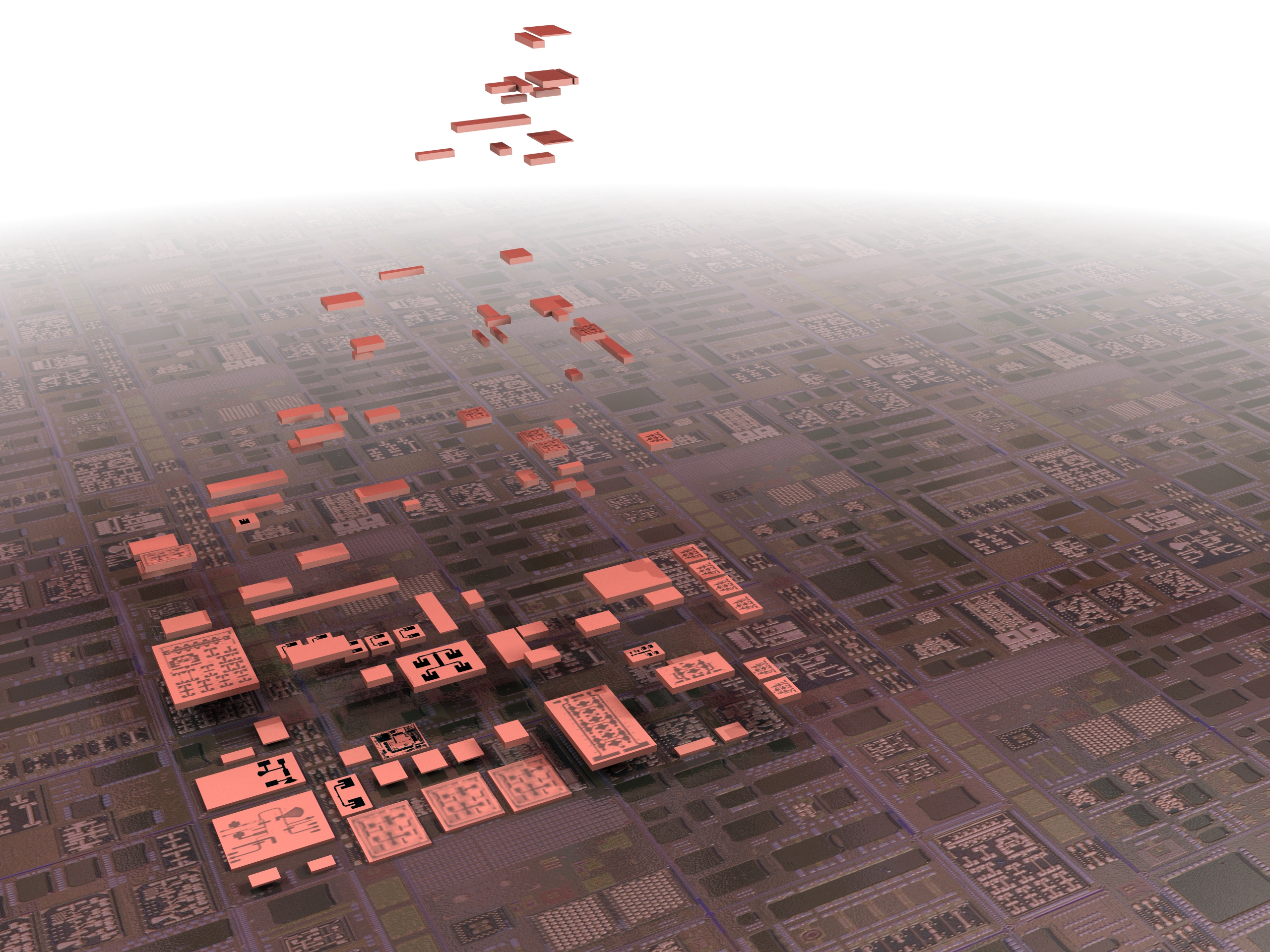
Reagan Institute warns of “inadequate” investments, “exceedingly fragile” supply chains, and “insufficient” accountability of government officials, among other US weaknesses.
By Brad D. Williams
The contract award is the first phase in the DoD’s Rapid Assured Microelectronics Prototypes – Commercial (RAMP-C) program, which is intended to bolster US-based commercial foundries.
By Brad D. Williams
“Throughout the pandemic, US adversaries like China weaponized supply chain vulnerabilities in a way that threatened Americans’ health and security,” warned Rep. Mike Gallagher.
By Brad D. Williams
“From the DoD’s perspective, they’re highly dependent on [Asia] for fabrication and packaging [of chips],” Hudson Institute’s Bryan Clark tells Breaking Defense. This has led to DoD calls to address a “fragile and threatened” chip supply chain.
By Brad D. Williams
“Once a chip is designed, adding security after the fact or making changes to address newly discovered threats is nearly impossible,” explains a DARPA spokesperson.
By Theresa Hitchens