WASHINGTON: DARPA has launched a four-year project to find ways to design security features into microchips as they are being made to help ensure the future supply chain.
While the name of the project is daunting — Automatic Implementation of Secure Silicon (AISS) — and the technical requirements are a serious challenge, the concept is pretty simple.
“AISS aims to automate the process of incorporating security into chip designs, making it easier and potentially more cost effective for any organization with even a small design team (start-ups, mid-size companies, etc.) to build security measures into their designs,” a DARPA spokesperson told Breaking D today.
“Overall, with AISS DARPA aims to bring greater automation to the chip design process to profoundly decrease the burden of including security measures,” the spokesperson said.
The two winning teams, according to a May 27 DARPA press release, are:
The two AISS research teams are:
- Synopsys, Arm, Boeing, Florida Institute for Cybersecurity Research at the University of Florida, Texas A&M University, UltraSoC, and the University of California, San Diego
- Northrop Grumman, IBM, University of Arkansas, and University of Florida
“Research and development on the $75 million program was commenced two weeks ago and incremental capabilities are expected to roll out to the chip design community over the next four years,” the spokesperson said in an email. “Our hope is that many of the capabilities will start appearing as features in commercial design automation software before the program completion.”
Digital integrated circuits are the engines that drive modern computers, and everyday digital devices such as smart phones. They are critical to the evolution of the Internet of Things (IoT). As such, they increasingly have become a key target of hacking by US adversaries and cyber criminals alike, DARPA explains. 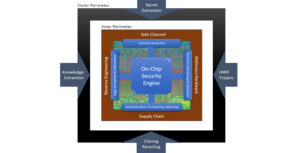
“Threats to IC chips are well known, and despite various measures designed to mitigate them, hardware developers have largely been slow to implement security solutions due to limited expertise, high cost and complexity,” the DARPA release says. “Further, when unsecure circuits are used in critical systems, the lack of embedded countermeasures exposes them to exploitation.”
Indeed, the Department of Commerce on May 15 took another swipe at Chinese telecoms behemoth Huawei and tightened its earlier efforts to block it from exporting its semiconductors and products to the US and allies. The Trump administration alleges that Huawei’s hardware and software, in particular that related to 5G wireless technology, are full of deliberate security holes in order to enable Chinese government spying. The ruling by Commerce’s Bureau of Industry and Security, which will take effect in September, seeks to prevent companies around the world from using American-made software and machinery develop chips for Huawei or its subsidiary firms.
The problem for device-makers, particularly in the IoT world where the market is largely for commercial products (think smart refrigerators), is that fixing potential security holes often isn’t seen as worth the time, effort and most importantly, money.
“The inclusion of security also often requires certain trade-offs with the typical design objectives, such as size, performance, and power dissipation,” the DARPA spokesperson said. “For example, something like a sprinkler isn’t likely to require the highest level of security protections. Investing in security mechanisms that take up a lot of space on the underlying chip, or significantly impact chip performance likely doesn’t make sense based on the sprinkler’s expected use and application.”
And yet, that future IoT sprinkler also will be other IoT devices and computer networks in operation by an individual, a company or a facility, such as a weapons depot.
Even more unfortunately, the spokesperson explained, “modern chip design methods are unforgiving – once a chip is designed, adding security after the fact or making changes to address newly discovered threats is nearly impossible.”
Thus, the AISS program is aimed at spurring research into two areas that can address four types of microchip vulnerability, the release says: “side channel attacks, hardware Trojans, reverse engineering, and supply chain attacks, such as counterfeiting, recycling, re-marking, cloning, and over-production.”
The first area of research will be focusing on “development of a ‘security engine’ that combines the latest academic research and commercial technology into an upgradable platform that can be used to defend chips against attacks, and provide an infrastructure to manage these hardened chips as they progress through their lifecycle,” DARPA said.
The second area, led by software specialists Synopsys, “involves integrating the security engine technology developed in the first research area into system-on-chip (SOC) platforms in a highly automated way,” the DARPA release said. The Synopsys team also will be working on how to integrate new security designs and manufacturing tools with currently available off-the-shelf products.
Nicholas Paraskevopoulous, sector VP for emerging capabilities development at Northrop Grumman, said in a May 27 press release that the firm’s “design tools will enable the development of secure and trusted integrated circuits with reduced costs.” Northrop Grumman is involved in the first AISS research area.
Synopsis could not be reached for comment by press time.
In a Taiwan conflict, tough choices could come for Big Tech
Washington could do more to incentivize tech companies to distance themselves from China, but CEOs should examine how they’d react to a fight in the Pacific, CSET’s Sam Bresnick and Emelia Probasco argue.