

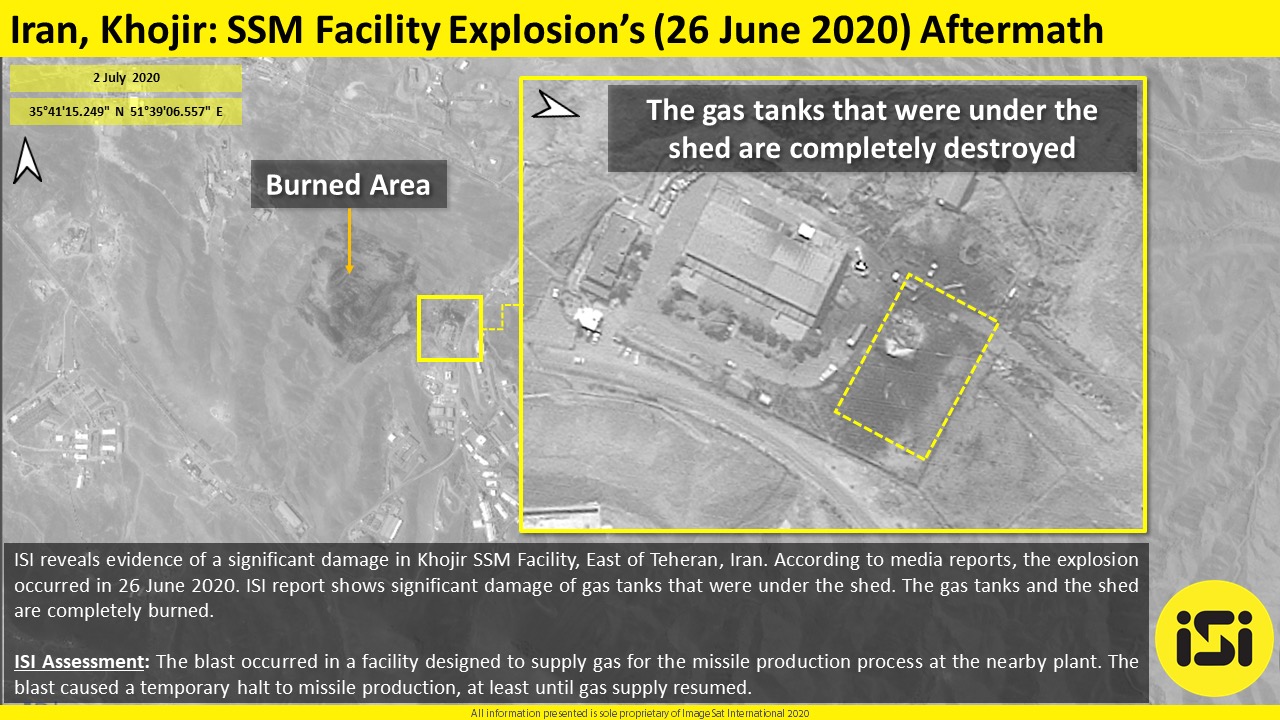
Iranian officials confirmed damage to a building built near the Natanz nuclear power plant today, saying an “accident” occurred. Israel has denied any connection to the huge explosion in the secret facility.
By Arie Egozi
GEOINT: Director of National Intelligence James Clapper identified China today as “the leading suspect” in the two sweeping hacks of the Office of Personnel Management, one day after NSA Director Adm. Mike Rogers dodged the issue. In Clapper’s first answer to a question about who is responsible for the OPM hacks, he laid the blame squarely on China. “On the…
By Colin Clark
WASHINGTON: Many a mother has warned roughhousing children that “it’s all fun and games until somebody loses an eye.” On Monday, four cybersecurity experts (two Americans and two Brits) agreed that the online attacks we’ve seen so far are all either espionage or sabotage: It doesn’t count as war until somebody dies. We have…
By Sydney J. Freedberg Jr.CAPITOL HILL: Maybe cyberspace isn’t as fragile as it’s made out to be. “Relax, Chicken Little, the sky isn’t falling,” said Columbia professor Abraham Wagner. “Protection ultimately is easier than penetration.” Wagner’s argument reverses the conventional wisdom that the attacker always has the advantage online. A forthcoming study by the Cyber Conflict Studies Association, for…
By Sydney J. Freedberg Jr.WASHINGTON: Rep. Mike Rogers, chairman of the House intelligence committee, cast doubt today on reports that the Stuxnet and Flamer viruses were the work of the US and Israel. In fact, he argued, it’s against America’s interest to be staging any cyber attacks because the US is so vulnerable to retaliation. “Don’t believe everything you…
By Sydney J. Freedberg Jr.CAPITOL HILL: The number of malware attacks soared 81 percent last year, from three billion in 2010 to five-and-a-half billion in 2012, Symantec senior engineer Patrick Gardner told congressional staff in a briefing here today. But those raw numbers aren’t the really bad news. What’s truly scary is the endless inventiveness of the attackers. They…
By Sydney J. Freedberg Jr.The Stuxnet computer worm that damaged Iranian nuclear facilities – widely suspected to be an Israeli or even U.S. covert action – was a model of a responsibly conducted cyber-attack, said the top lawyer for the U.S. military’s Cyber Command, Air Force Col. Gary Brown. By contrast, the Chinese stance, which holds that the international…
By Sydney J. Freedberg Jr.





















Technology is moving too fast to keep track of everything, but there’s one overarching trend that policymakers must not miss in 2015. Call it “convergence.” Cybersecurity is no longer its own specialized function for tech geeks to take care of off to one side while the rest of the organization gets on with the real…
By Michael Warlick