“Strategic competition is alive and well in cyberspace, and we’re doing it every day with persistent engagement,” the CYBERCOM and NSA leader said.
By Brad D. Williams
“I have a mantra of ‘I want to kill to the [Common Access Card] as the primary authentication mechanism for the department’,” Lt. Gen. Robert Skinner said. “Industry has better authentication, and it’s not just two-factor, it’s truly multi-factor authentication.”
By Brad D. Williams
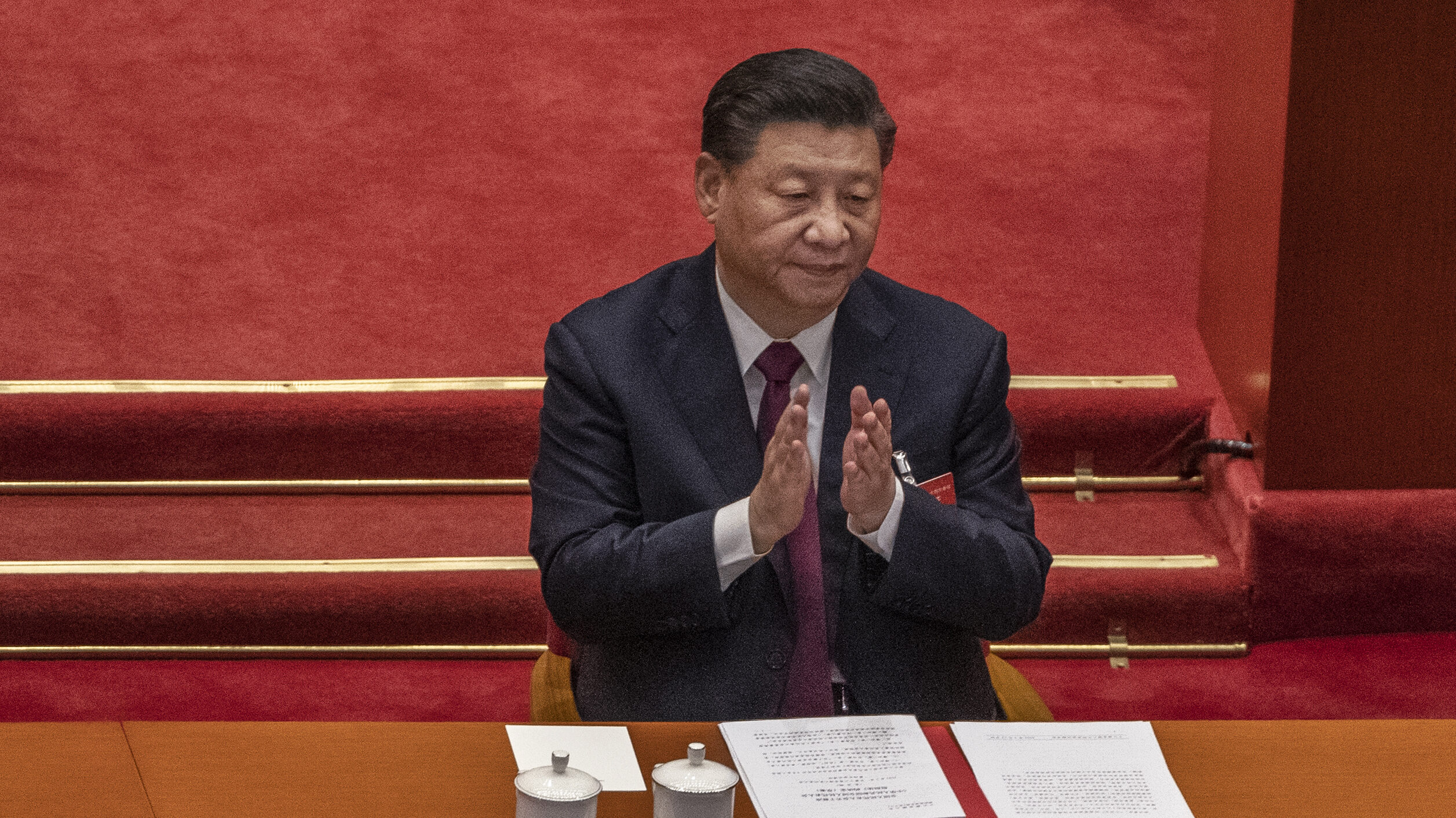
The law’s vulnerability disclosure provisions will give the Chinese government a head start on remediating — and potentially exploiting — zero-day vulnerabilities, possibly to include those discovered in tech used by the Defense Department, Intelligence Community, and across the US public and private sectors more broadly.
By Brad D. Williams
“It’s part of a larger diplomatic strategy,” cyber policy expert James Lewis said of the US attribution to China for Microsoft Exchange hacks earlier this year.
By Brad D. Williams
“The PRC’s pattern of irresponsible behavior in cyberspace is inconsistent with its stated objective of being seen as a responsible leader in the world,” a senior administration official said on Sunday night.
By Brad D. Williams
The Exchange campaign attribution will also provide hints about the role of the first national cyber director in such incidents. NSA veteran Chris Inglis was confirmed for the position just weeks ago.
By Brad D. Williams
The cyber executive order “properly emphasizes” information sharing. Sens. Peters and Portman float updating FISMA. FERC calls for mandatory pipeline cyber standards. Report says vulnerable Exchange Server “most likely culprit” at Colonial. FireEye details DarkSide’s business ops.
By Brad D. Williams
“It reflects a fundamental shift in our mindset — from incident response to prevention, from talking about security to doing security,” a senior administration official says.
By Brad D. WilliamsZero-trust security “is not one single product that one can purchase off the shelf,” a NIST scientist observes. But underlying zero trust’s many component parts are a few critical elements, including identity and automation.
By Brad D. Williams
The patch secures a zero-day vulnerability disclosed last month and is just one of four vulnerabilities being actively exploited in Pulse Connect Secure.
By Brad D. Williams
“We are working with each agency to validate whether an intrusion has occurred and will offer incident response support accordingly,” CISA’s deputy executive assistant director told Breaking Defense.
By Brad D. Williams
“My hope is that we can create this structure… to get an early warning system,” the Senate Intel Committee chair said. “Voluntary sharing is no longer effective.”
By Brad D. Williams
Threat actors are targeting one newly discovered and three previously known vulnerabilities in Pulse Connect Secure enterprise VPNs, according to a CISA emergency directive and alert, as well as blog posts by FireEye and Ivanti. “There is no indication the identified backdoors were introduced through a supply chain compromise of the company’s network or software deployment process,” FireEye noted.
By Brad D. Williams
“The innovations… and the lessons learned from these responses will be used to improve future unified, whole of government responses to significant cyber incidents,” the White House says.
By Brad D. Williams