

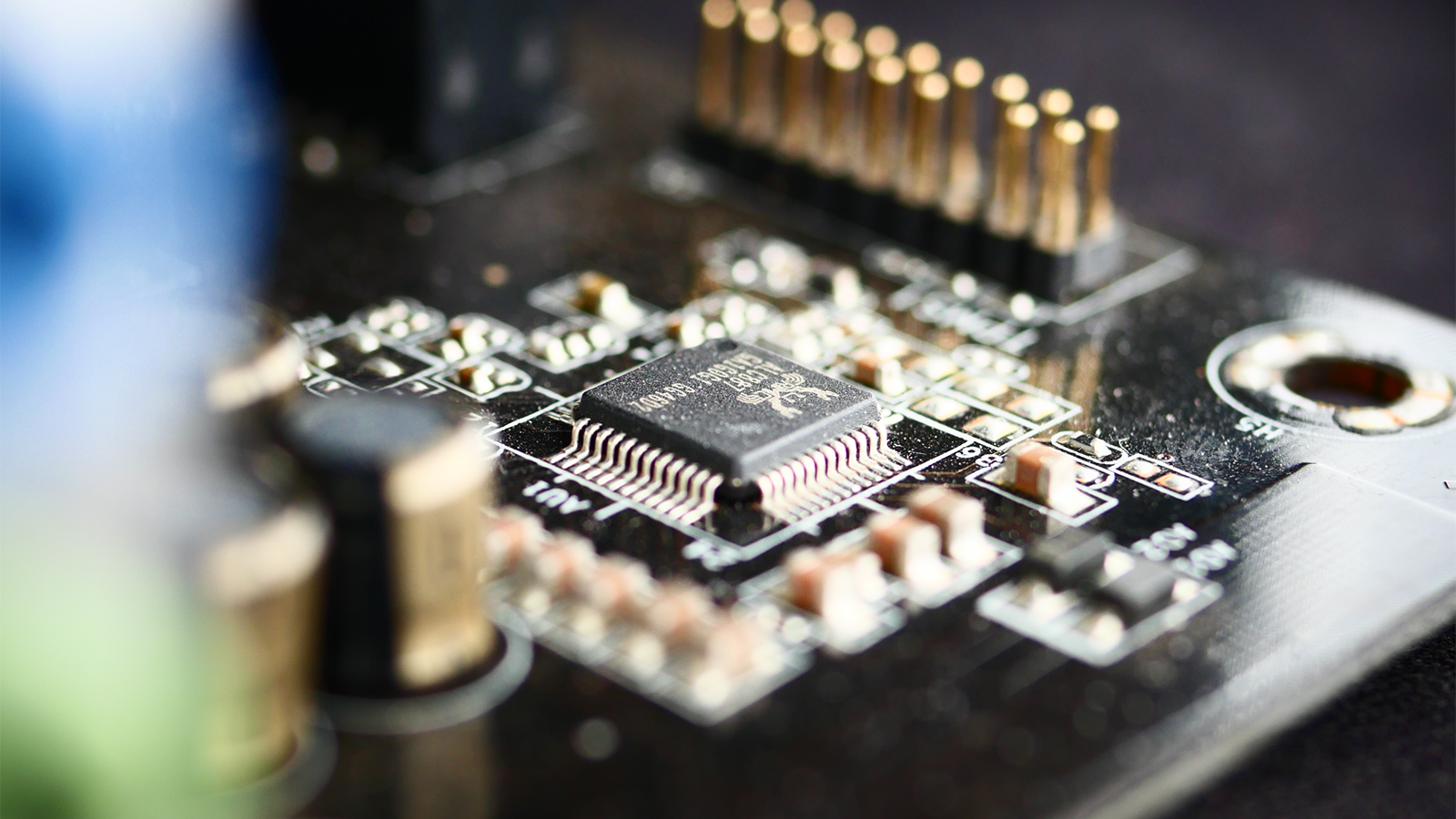
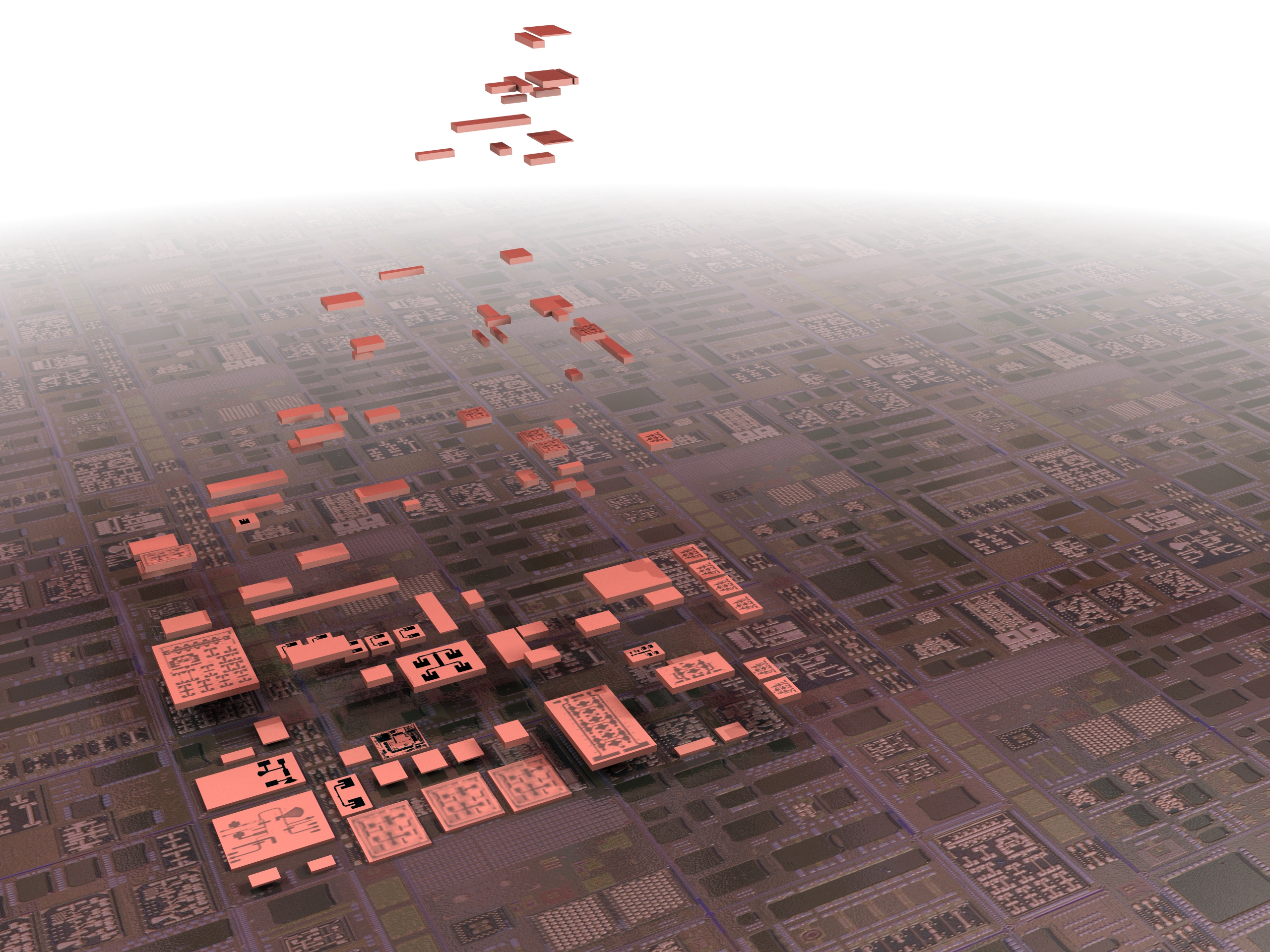
At a microscopic level, advanced semiconductors are packed with modular chiplets to meet dynamic needs of air defense, robotics, and satellites.
By Breaking Defense
With the delivery of the first set of prototypes, “the pendulum is swinging back to onshoring our own domestic capabilities,” Heidi Shyu, under secretary of defense for research and engineering, told reporters.
By Jaspreet Gill
Corell spoke on information and communications tech (ICT) supply chain risks on the same day DARPA and Intel announced a three-year partnership to develop and domestically manufacture new semiconductors for DoD applications.
By Brad D. Williams
How can Pentagon clouds process data quickly while it’s still encrypted, instead of having to decrypt it and thereby render it vulnerable?
By Kelsey Atherton
WASHINGTON: We’ve got bus-sized satellites that can probably see any blemishes on Chairman Mao’s badly rebuilt face from space (didn’t know about that, did you?). We’ve got U-2s with their superb sensors watching the Chinese coast (for now). We’ve got P-8s scanning the seas for Chinese submarines and testing their radar. Our subs — hopefully — cruise…
By Colin Clark
LATVIAN EMBASSY, WASHINGTON: “We are neighbors of Russia and we have always been realists,” Ambassador Andris Razans told me. “Sometimes we might be characterized as alarmists, troublemakers, etc., but I think we are realists.” Even as President Obama exchanges tense words with Vladimir Putin on the sidelines of today’s D-Day anniversary ceremony, many Americans and…
By Sydney J. Freedberg Jr.PENTAGON CITY: Hungry for answers on how to make more effective use of the tens of thousands of hours of video gathered by Predators, Global Hawks and other military eyes in the sky, Air Force officials recently visited NASCAR, the car racing people, to learn better and faster ways of mining video data. “We have…
By Colin ClarkChina unveils a new “stealth” jet, but we don’t know how stealthy it is or when it might fly actual missions. China unveils a new aircraft carrier. Its leaders boast about extending China’s reach, but the carrier doesn’t have any planes and we aren’t sure when they might build them. Monitoring a rapidly developing China,…
By Joan Johnson-FreeseWASHINGTON: Despite the tremendous impact unmanned systems are having on the battlefield, military leaders still struggle to get intelligence gathered from these systems into the hands of those who need it. The systems designed to stream raw data collected by the diverse fleet of unmanned systems in the field continued to hamstring combatant commanders and…
By Carlo Munoz(Photo: Central Intelligence Agency) WASHINGTON: Becoming a whistleblower is often a risky and difficult path for federal employees, and so is finding the truth and protecting those who have exposed wrongdoing from being fired, punished or harassed. Dan Meyer, director of civilian reprisal investigations with the Office of the Inspector General at the Department of…
By Carlo MunozCORRECTED: We Inflated The Value of Digital Globe’s Most Recent Government Contract San Antonio: You can smell the fear and worry here at the annual Geoint conference. The budget cuts that Director of National Intelligence Jim Clapper outlined yesterday may be as deep as $40 billion over the next 10 years, sources here say. The…
By Colin Clark

























Jarno Limnéll is the Director of Cyber Security at McAfee (now part of Intel), a PhD in military science, and a former officer in the famously tough Finnish armed forces, where he spent five years as a strategic analyst. He spoke to us in June about the Russian threat in cyberspace, which many analysts consider far…
By Jarno Limnell