IBCS sees more, understands better, and decides faster for a true transformational change for the US Army and its allies.
By Breaking Defense
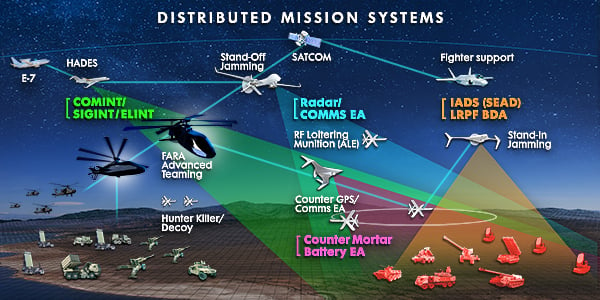
Survivability that spans the spectrum.
By BAE Systems
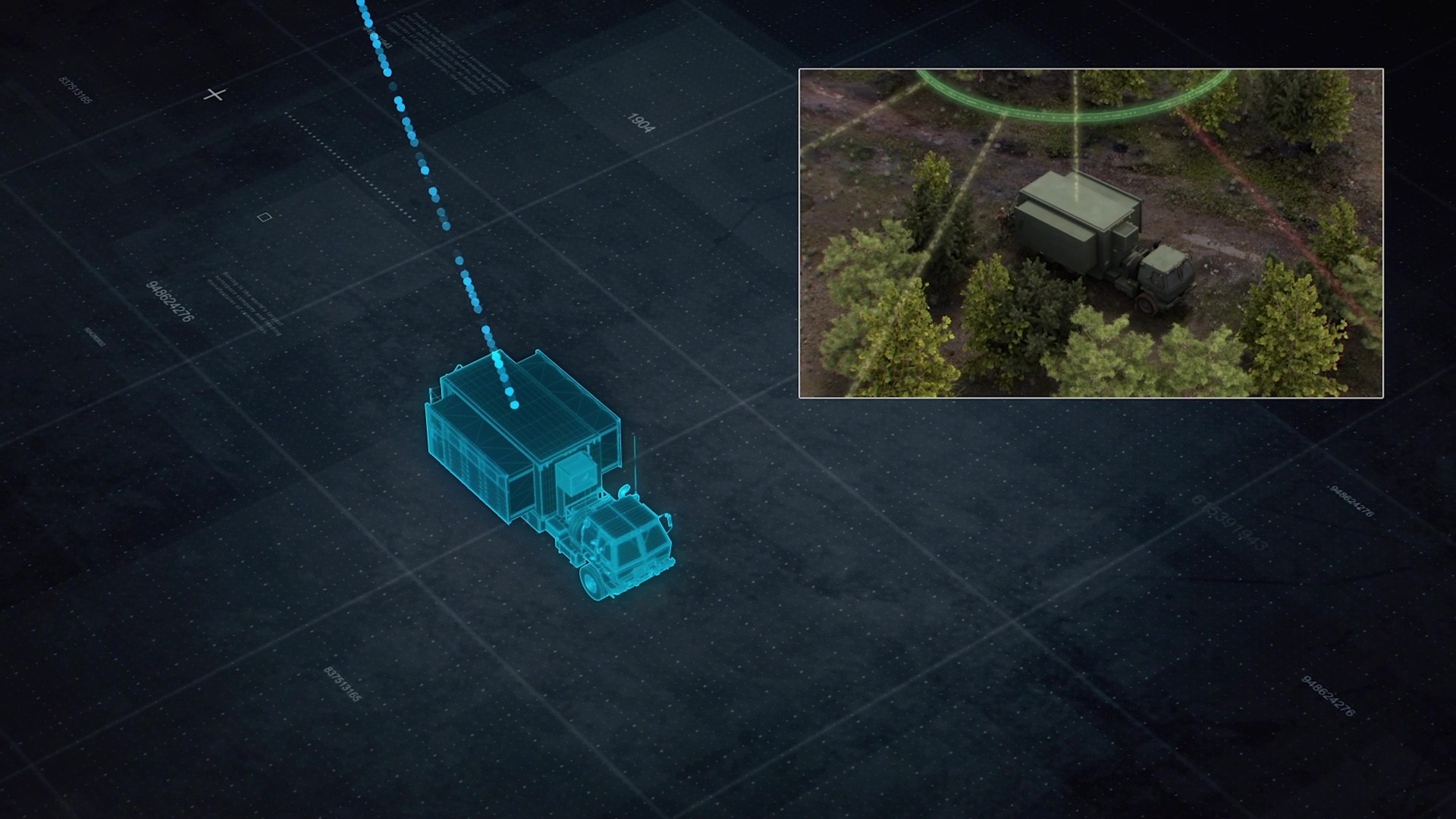
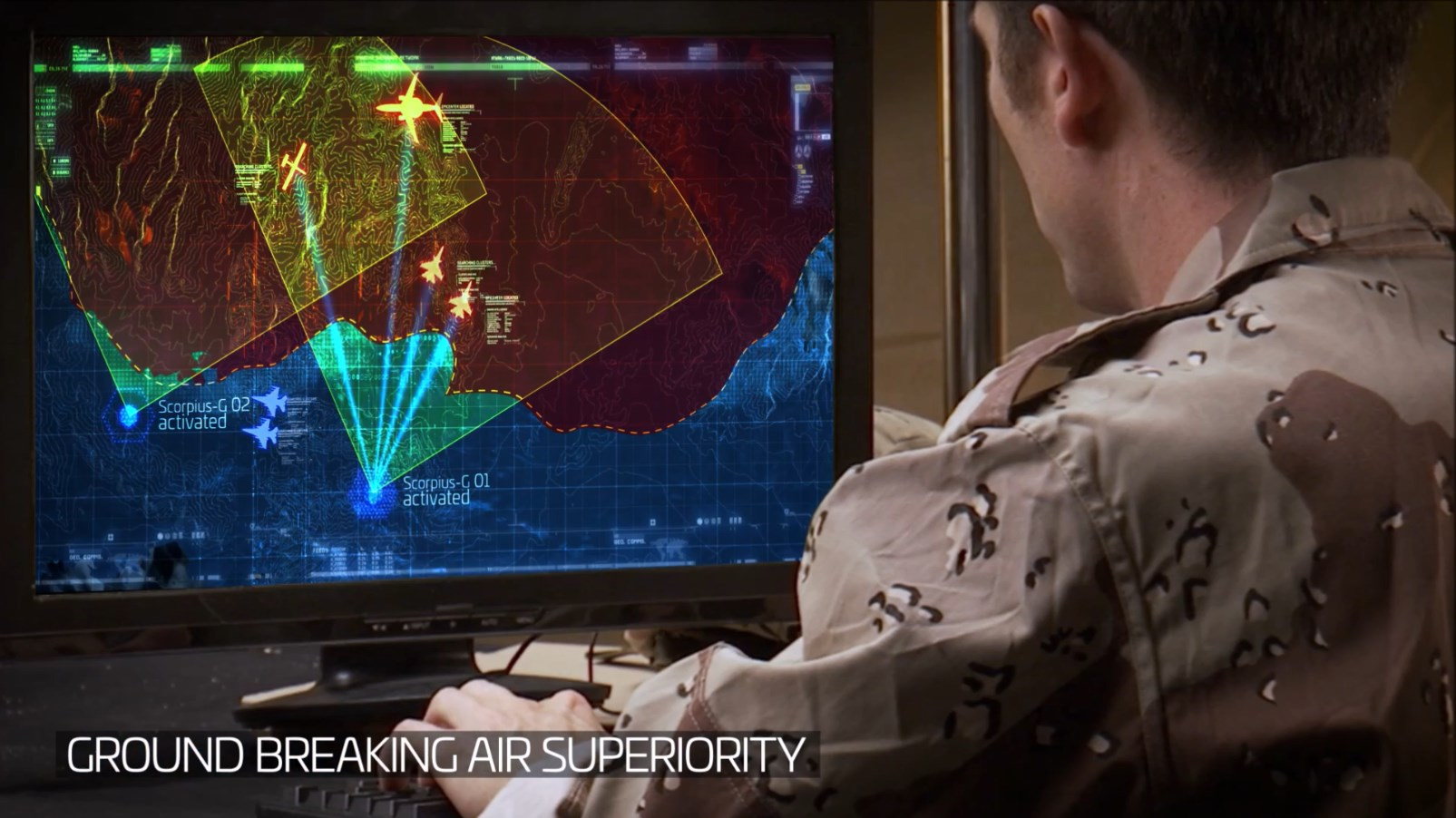
Scorpius systems revolutionizes electronic warfare with new lineup of cutting-edge solutions.
By ISRAEL AEROSPACE INDUSTRIES
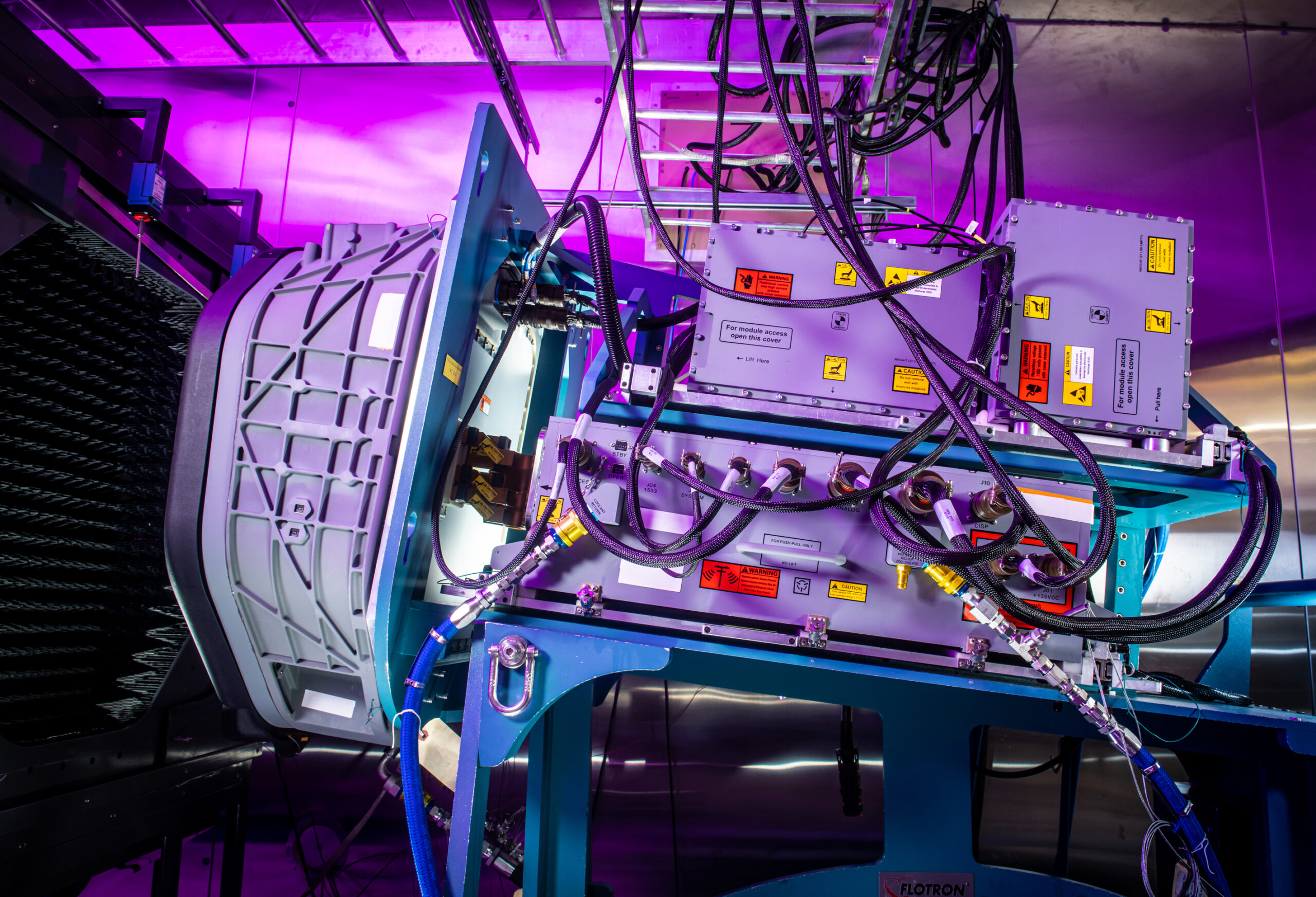
For Future Vertical Lift, the Army wants new and innovative technology that transforms their platforms into advanced weapons systems. One such technology is Raytheon Technologies’ revolutionary RAIVEN Turret 1000, first in a new family of EO/IR systems.
By Breaking Defense
To remove the human from the loop in uncrewed operations, the AI must be trusted to take specific actions every time certain scenarios happen based on its programming.
By Breaking Defense
Part 3 of a narrative series illustrating how Elbit America’s USA-manufactured products enable customers to successfully accomplish their most demanding missions.
By Elbit America
UAE companies like NIMR, EARTH, EDGE, and Abu Dhabi Ship Building work with Leonardo DRS to address Middle East threat scenarios.
By Breaking Defense
The key is creating intelligent gateways that connect networks and the cloud across security domains and translate data so the joint services can speak the same language
By Breaking Defense
On the 50th anniversary of the F-15 Eagle’s first flight and its groundbreaking APG-63 radar that helped the fighter revolutionize tactical combat, here’s a look at the state of radars and mission systems today.
By Breaking Defense
Army National Guard units are an essential part of the Total Force. They need the same equipment, too.
By General Atomics Aeronautical Systems, Inc.
Inside this free eBook, you’ll find a series of stories touching on a sample of key issues that crossed the desks of service leadership from the first half of 2022.
By Breaking Defense
Emerging threats and complex challenges to situational awareness require a next generation of sensor systems.
By Breaking Defense
Multispectral operations are the response to a dynamic world where hostile nations have well known and advanced capabilities in EW and cyber.
By Breaking Defense
The new pod takes the P-8 “and further expands it to be truly multi-int and multi-spectral,” a Boeing rep said.
By Colin Clark