
How a key Pentagon tech leader plans on ‘blowing up’ outdated software risk framework
In an exclusive interview, Katie Arrington, who is performing the duties of the DoD CIO, makes the case for the new Software Fast Track (SWFT) program.

In an exclusive interview, Katie Arrington, who is performing the duties of the DoD CIO, makes the case for the new Software Fast Track (SWFT) program.

Beginning as a $26 million, two-year pilot project, the NCODE enclave will offer CMMC-compliant “cybersecurity as a service” for smaller firms that can’t protect themselves against advanced threats, said Army Undersecretary Gabe Camarillo.

As the Defense Department and Congress strive to streamline clumsy Authorization To Operate (ATO) procedures for software, the Pentagon also needs more computing infrastructure to test and experiment with new code.

The legislation proposes that if one office in the department officially deems a "cloud-based platform, service, or application" is sufficiently cybersecure to use, then all parts of DoD can accept this ATO.
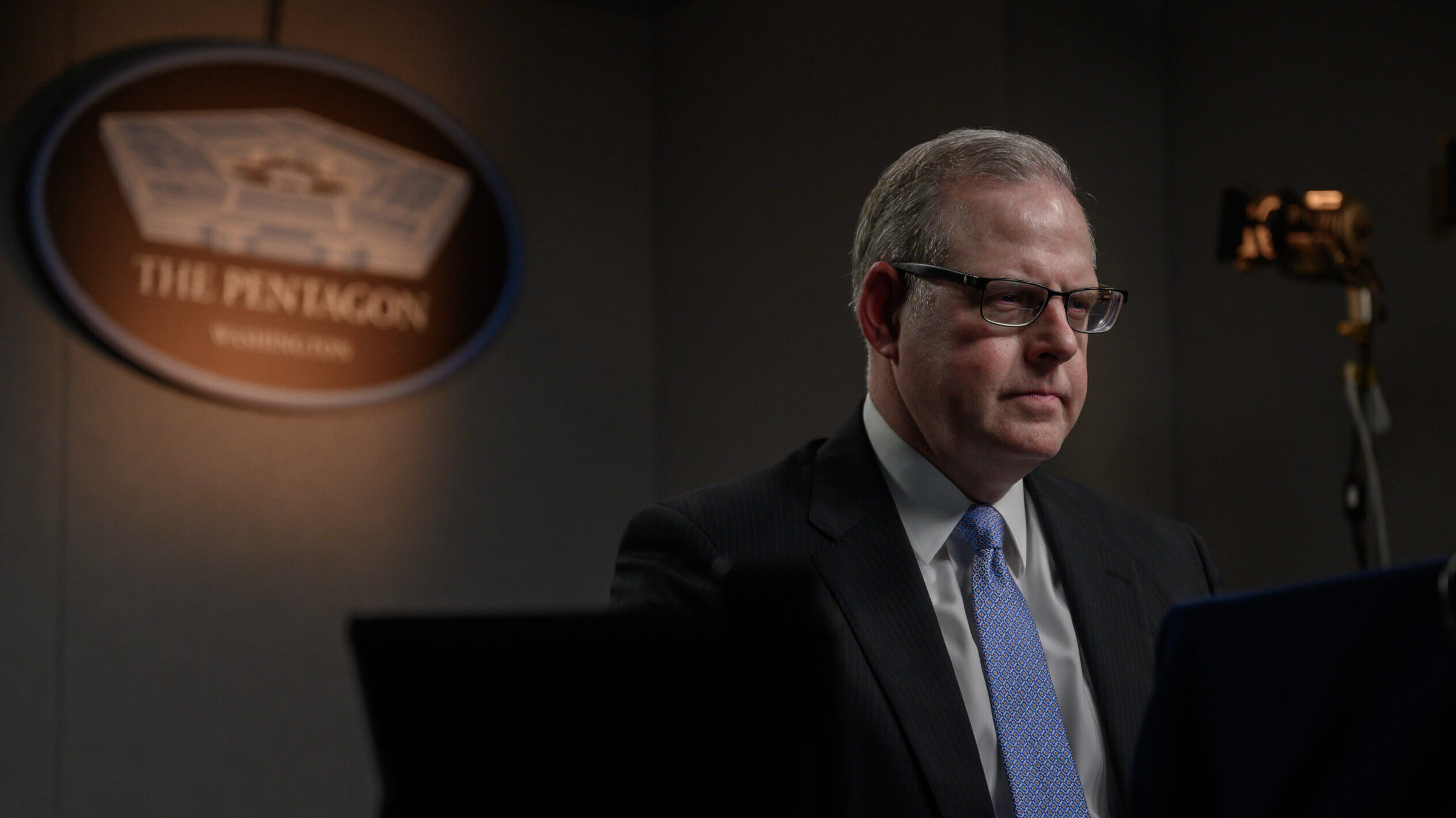
“We’ve heard you loud and clear on this within the DoD. I’m not going to say this is going to solve every bit of it, but it’s going to help us a bit,” Pentagon CIO John Sherman said.

"We view cybersecurity as a compliance problem. And it is most definitely not a compliance problem," Navy Chief Information Officer Aaron Weis said, arguing the service must shift to a "readiness" focus.

OSCAL's goal is to enable compliance and security assessments to keep pace in complex, fast-moving, ever-changing DevSecOps environments.